Why DNS over HTTPS (DoH)?
DNS serves as the Internet's phonebook, converting human-readable domain names into machine-readable IP addresses. By default, DNS queries and responses are transmitted in plaintext using UDP, making them susceptible to interception by networks, ISPs, or anyone with the ability to monitor transmissions. Even if a website employs HTTPS for secure communication, the DNS query essential for accessing that site remains exposed.
The absence of privacy in DNS has significant implications for security and, in certain instances, human rights. When DNS queries lack privacy, it becomes simpler for governments to enforce Internet censorship and for attackers to surveil users' online activities.
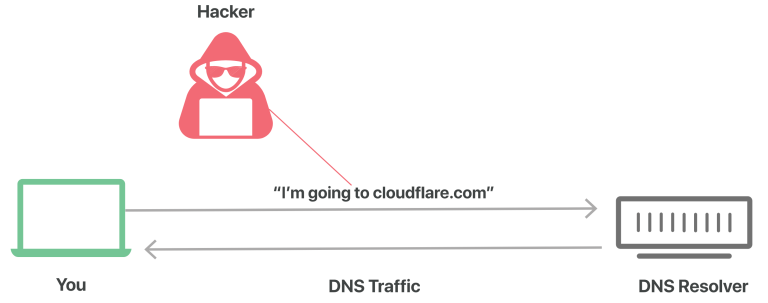
Consider a regular, unencrypted DNS query as analogous to a postcard sent through the mail: anyone handling the mail might catch a glimpse of the text on the back, making it unwise to send sensitive or private information on a postcard.
DNS over HTTPS are two standards designed to encrypt plaintext DNS traffic, preventing malicious entities, advertisers, ISPs, and others from interpreting the data. To extend the analogy, these standards aim to encase all postcards in an envelope before sending them through the mail. This way, individuals can send postcards without worrying that someone might be snooping on their activities.
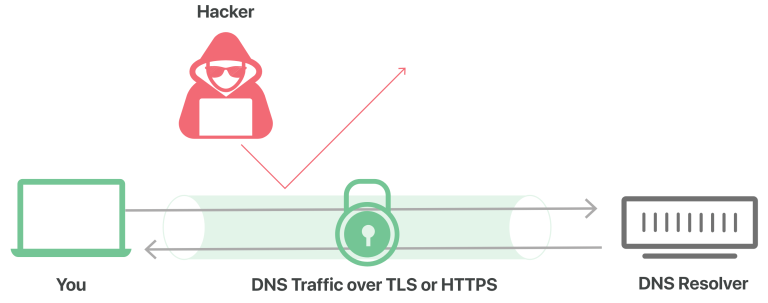
DNS over HTTPS, abbreviated as DoH, serves as an alternative to DNS over TLS (DoT). In DoH, DNS queries and responses undergo encryption, but they are transmitted through the HTTP or HTTP/2 protocols instead of directly using UDP. Similar to DoT, DoH ensures that attackers cannot forge or tamper with DNS traffic. From the perspective of a network administrator, DoH traffic resembles other HTTPS traffic, such as typical user interactions with websites and web applications.